Who is Pangu Team?
Pangu Team is a well-known security research group that has released multiple exploits and complete jailbreaks before, back on iOS 7, iOS 8, and iOS 9 times. They are nowadays focused on security research and they still do iOS hacking, demonstrating a brand new jailbreak almost every year, and usually for the latest version of iOS.
The Pangu Jailbreak started as an untethered jailbreak for iOS 7 back on iOS 7.1.2 days, and it has since progressed. On iOS 9.3.3, however, Pangu Team has moved to the IPA-based jailbreaks, the same type that Unc0ver and Taurine Jailbreak are nowadays.
The last public jailbreak released by the Pangu Team was the iOS 9.2 – iOS 9.3.3 64-Bit jailbreak which was semi-untethered.
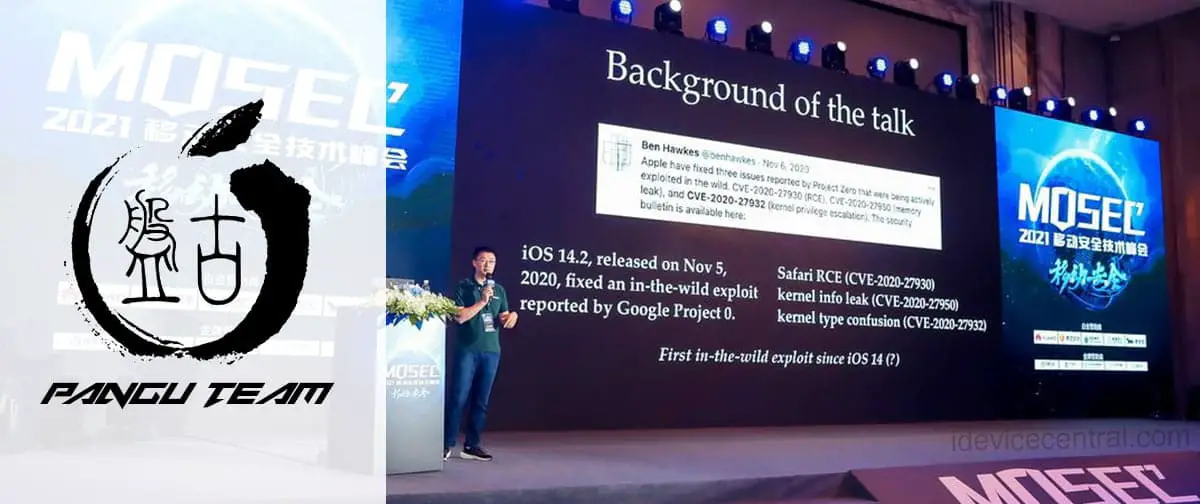
New iOS 15 Beta 4 Jailbreak Achieved by Pangu Team at MOSEC 2021 For iPhone 11 Pro
Pangu Team, together with PoC (Power of Community) organize the MOSEC conference (Mobile Security Conference) every year.
This year, Pangu Team had its own member as a speaker. Tielei Wang, a Pangu Team member, had a presentation called “Exploitations of XNU Port Type Confusion”. The XNU is the kernel behind iOS, macOS, tvOS, iPadOS, and watchOS.
@WangTielei is giving his talk “Explorations of XNU Port Type Confusion.” #MOSEC2021 pic.twitter.com/3AjmWn6MG0
— vangelis (@vangelis_at_POC) July 30, 2021
The MOSEC 2021 speakers page states the following about the presentation by Tielei:
In this talk, we will continue to analyze this vulnerability and discuss its giant attack vector. Based on this type confusion primitive, we will explore different ways to trigger other kernel memory corruption issues including UAF, overflow and out-of-bounds access, and also bypass the sandbox to access any Mach services on iOS.
As such, we can see Pangu Team does have multiple Kernel exploits, including User-After-Free types.
According to the official MOSEC account on Weibo, Pangu Team has demonstrated a full iOS 15 Beta 4 jailbreak working on iPhone 11 Pro. This is important because it represents the very first jailbreak to be achieved and demonstrated publicly for iOS 15 which is currently in Beta.
There’s also another, more important side to this story that many seem to miss. The device that was successfully jailbroken was an iPhone 11 Pro. This is by no means an easy feat because every device after iPhone X, this means iPhone XS / XR, iPhone 11, iPhone 12, and iPhone SE 2020, have what is called PAC or Pointer Authentication Codes.
PAC is hardware-level security mitigation that prevents many common exploit techniques from being usable because the memory addresses on the device are tagged, thus eliminating the possibility to easily jump to the addresses you want.
Pointer Authentication Codes (PAC) and iOS
This security mitigation introduced in A12 (iPhone XS / XR) has indeed added complexity to the jailbreak development. Not only now Kernel exploits are harder to build (thanks to fewer exploit techniques being available), the post-exploitation for jailbreak purposes (i.e. patching Sandbox, AMFI / CodeSign, ROOT access / R/W FileSystem) also requires dealing with PAC in a way or another.
- This has been successfully tackled in iOS 14 by Taurine Jailbreak and Unc0ver via PACless approaches, but it’s unclear how Pangu Team has done it.
What does this mean for the Jailbreak community?
Pangu Team’s achievement at MOSEC 2021 could be interpreted at first as a reassurance that iOS 15, although new and improved, did not change enough security-wise to make jailbreaking harder than it already is.
It also means that for a skilled security researcher, no amount of Apple’s shenanigans when it comes to new security mitigations for jailbreak prevention is too much.
As for the release, it’s unclear whether Pangu Team will release the details about this vulnerability, but if they decide to do so, I wouldn’t expect it until the vulnerability is fully patched in iOS 15, either in the Beta or in the stable (GM) release.
Pangu does keep a blog online where they do post vulnerability/exploit write-ups nowadays. It may be the case that the vulnerability will be released as a write-up once patched. If they do release it, it will definitely be great for the jailbreak community, but it’s unknown for now.
As always, you can find the latest iOS Jailbreak Downloads on our website.
Photo courtesy of @vengelis_at_POC


Leave a Reply
You must be logged in to post a comment.